Review: Meerkat (SSH Tunnels Made Easy)
Back in May I did a bit of traveling and became somewhat paranoid about the Internet connections I found at various hotels. I began using SSH tunnels to protect my web traffic when using Internet connections I did not trust. While setting up an SSH tunnel is a fairly trivial matter for those familiar to the command line, it's not the same for everyone. Meerkat, from the developer that brought you Pukka, makes using and managing ssh tunnels easy.

How To Use Meerkat
Create an account with your server. You'll need SSH access but you probably already have that.
Add an SSH tunnel. I created one with dynamic port forwarding and will use it for all my web traffic.

OS/Browser Configuration
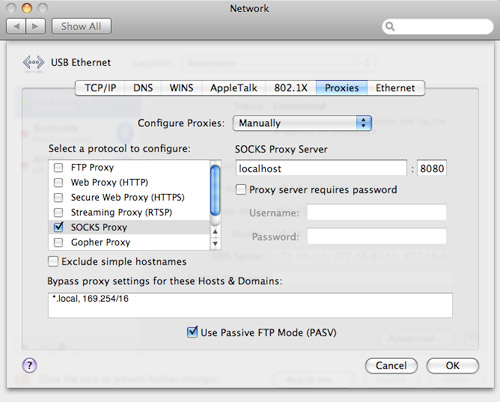
Go to the main Meerkat window and ensure that there is a check in the box marked "Active." The SSH tunnel should now be active, but your browser and OS need to know that it's there so they can use it.In OS X, head over to System Preferences » Network » Advanced » Proxies. Check the box next to SOCKS Proxy, type in "localhost" with port 8080 for the server and click OK, then Apply. Safari should now be utilizing the SSH tunnel.
To get Firefox 3 to use the tunnel, go to Preferences » Advanced » Network » Settings and select the manual proxy configuration radio button. Enter in localhost and port 8080 for SOCKS Host.
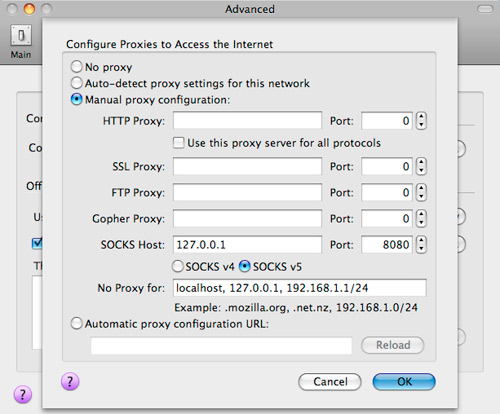
I recommend using Firefox 3 when browsing with an SSH tunnel since it uses remote DNS by default (network.proxy.socks_remote_dns = true in about:config). Basically, with a SOCKS 5 proxy Firefox can determine which side of the proxy handles DNS work. If done locally, people snooping around your network traffic can still see what domains you're browsing, although they won't see particular URLs. The remote DNS setting ensures that your trusted server takes care of all DNS lookups.
Testing
You can test to see if the tunnel is working by visiting a site like What Is My IP. If the IP address listed is that of your server, you're good to go. The only downside of SSH tunnels is the longer distance and inherit latency issues that your web traffic incurs. For example, my bandwidth more than halved when the SSH tunnel was active. That's the price of security though.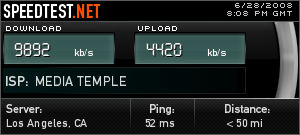
Thoughts on Meerkat
Meerkat is unobtrusive (I prefer disabling the dock icon and just have a menubar icon) and makes using SSH tunnels easy. You don't have to fire up a command line or write a script to automatically create a tunnel when you want to use it. You only need to turn on Meerkat. Whether that functionality is worth the 20 license cost is up to you.Other Meerkat features I haven't yet tinkered with include Growl notifications, Bonjour service advertising (make a tunnel and let other networked Macs access it over Bonjour) and application triggering (have Meerkat open whatever app you like when an SSH tunnel is created).
Do you browse on untrusted networks from time to time and use SSH tunnels to add in security? Would you use Meerkat?